So, you’re feeling the urge and longing for intimacy. Perhaps you’re fantasizing about someone or exploring your desires. If any of these apply to you, then you’ve come to the right place. I’m about to reveal some of the steamiest resources to satisfy that craving right now.
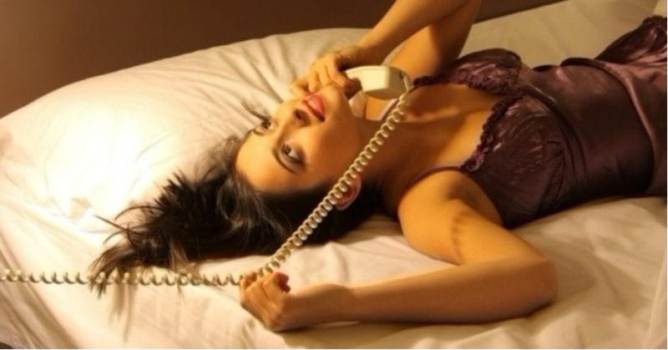
If you’re wondering how, then say “hello” to phone sex. Let me tell you a little bit about myself. My name is Hayley, and I’m from Miami. I used to work part-time as a phone sex operator, mainly to pay for my college degree.
It was a wild yet profitable venture for me, and it helped me make ends meet.

One thing I learned from being a phone sex operator is that I needed to be engaging and responsive. My goal was to keep my clients satisfied and eager for more until they reached their peak.
Indeed, there were plenty of dirty talk, enticing sounds, and role-playing elements to make it all feel real. I strived to accommodate my clients’ fantasies and go along with their fetishes – whatever they might be. That’s the nature of phone sex.
Why People Call for Phone Sex
There are many reasons why people prefer phone sex. One obvious reason is because they’re in the mood and craving intimacy. Another reason is the anonymity it provides, allowing them to engage in dirty talk and moaning without anyone knowing their identity. Additionally, it’s often considered a small price to pay for a quick and satisfying experience.
For those who just want to have fun, dating can be expensive and even impractical. Consider the cost of a meal at a decent restaurant, a movie, and drinks afterward.
What are the chances of getting intimate after spending so much? So, many people, primarily men, bypass all the fuss and go straight to the action by calling phone sex services or the chat line numbers.
Essentially, it’s for pure sexual pleasure through mutual masturbation with a phone sex partner who can make the experience feel real and incredibly satisfying.
Types of Phone Sex
Phone sex is an umbrella term for a variety of sexual interactions using a phone line. Here are the most common types;
Phone Sex Between Couples
Couples in long-distance relationships or those looking to explore new forms of intimacy often engage in phone sex. It’s a way to satisfy each other’s physical needs, regardless of distance or other factors.

For some, phone sex is a way to explore fantasies or keep the spark alive in their sex lives. It can act as a type of foreplay, creating a strong desire for each other and building anticipation for passionate encounters later on.
Phone Sex Hotlines
Phone sex as a commodity can be found in the form of phone sex hotlines. These involve phone sex operators who are paid on a per-call or per-minute basis.
This exchange of payment demonstrates that phone sex has evolved into a commercial activity. It has grown into a widespread business between customers seeking sexual pleasure (primarily men) and providers (phone sex operators, who are mostly women).
Essentially, phone sex hotlines serve as a type of customer service that offers sex over the phone. Based on my own experience as a phone sex operator, approximately 90% of callers are men.

Phone Sex Chat Lines
Picture a one-night stand, hookup, or intimate encounter with a stranger – but virtually, over the phone, and completely anonymous. That’s what phone sex chat lines offer. They facilitate phone sex between real callers within a local area, without involving phone sex operators.
These chat lines are similar to dating apps and websites, as the callers are genuine individuals (primarily adult singles) searching for someone to engage in phone sex with. Phone sex chat utilize a toll-free number that allows callers to access a shared system. Here, they can select a chat partner for a private conversation.
Most companies promoting phone sex provide free trials to first-time users. After the trial period, chat packages can be purchased online or through a customer service hotline for direct assistance.

How Phone Sex Works
Phone sex involves engaging in sexually-stimulating conversations to arouse both parties, often leading to mutual masturbation. Imagination and role-playing are crucial components for participants during the act.
As a phone sex operator, virtual sex can be quite challenging if my client struggles to visualize the erotic images in their mind.
Imagination is key to pleasure, and the explicit conversation between us over the phone should be paired with sexual fantasies and masturbation to achieve the desired experience.
Dirty Conversations
Phone sex conversations can take various forms, including guided fantasies, erotic confessions, seductive narratives, and sensual commands.
Stories that convey intense pleasure are also crucial, along with provocative questions that can ignite arousal. I once had a client who introduced himself as a public adjuster from Miami with a strong attraction to one of his clients.
He shared his fantasies of the woman performing oral sex in exchange for insurance approval. In the heat of the moment, he eagerly asked me to scream his name and beg for him.

Role Playing Elements
Role-playing elements related to one’s sexual desires and fantasies can set the theme for phone sex. You can create imaginary scenarios, such as a boss having sex with their secretary on an office couch or a doctor engaging in steamy encounters with patients. Exploring your naughty fantasies can heat up the phone lines, potentially leading to both of you passionately calling out each other’s names in intense pleasure.
Sexual Attitude
Throughout my time as a phone sex operator, I’ve encountered various types of male callers with different attitudes towards sex. Some are aggressive, while others are passionate. There are also those who feel awkward, and part of my job is to build up the heat and guide them towards a satisfying and mind-blowing conclusion.

I generally perform at my best when my client is responsive and engages in dirty talk. Even after working as a phone sex operator for a couple of years, there are still clients who can genuinely turn me on. To be honest, I’ve had my own share of satisfaction because some calls have provided me with truly mind-blowing experiences.
Audible Expressions of Pleasure
In phone sex, every word and sound you make significantly impacts the experience. Gentle moans, cries of delight, deep sighs, and breathing sounds can all heighten arousal levels. Each moan in response to stimulation, along with the sounds your body makes, contributes to sexual satisfaction.
It’s essential to maintain the dirty talk, consistently express your pleasure, and continuously touch and caress your intimate areas to make it sound natural. So, phone sex is about giving, receiving, and creating appropriate responses at every step to ensure a pleasurable experience for both parties.

Tips to Have a Good Phone Sex Experience
Whether you’re considering a job as a phone sex operator or simply want to try phone sex with someone, it’s essential to be well-prepared. Engaging in phone sex with someone you know differs from doing it with a complete stranger. Likewise, having phone sex for pleasure is different from doing it for money.
Regardless of your intentions, our tips will help you make the experience gratifying and rewarding.
Here are some basic tips when having phone sex;
- Be willing to talk dirty. Be ready to use words like cock, dick, pussy, clit, cum, suck, nipples, horny, and fuck, among other explicit and sexually suggestive terms.
- Be expressive. Prepare to convincingly moan, sigh, whisper, and take deep breaths. The sounds you make should effectively convey pleasure.
- Don’t reveal your identity. Whether you’re working as a phone sex operator or using chat lines to satisfy your desires, never disclose personal or private information.
- Go all the way. If you feel an orgasm coming during phone sex, indulge yourself. It’s not every day that you find a compatible phone sex partner.
- Practice faking an orgasm. As a phone sex operator, when I sense my client is about to climax, I use my acting skills to fake an orgasm, providing them with a satisfying ending.

Tips to Become a Phone Sex Operator
Becoming a phone sex operator is a fitting job for those seeking extra income, flexible hours, and an opportunity to work creatively in the erotica industry from the comfort of their home. If you’re considering entering this field, remember that it’s not for the faint-hearted or narrow-minded.
Being open-minded and understanding that you are working within an adult industry and selling sexual experiences is essential for success in this line of work.

Qualifying Process for Phone Sex Operators
- You must go through an interview and audition process.
- You must be willing to entertain callers with a variety of kinks and fetishes.
- You must be willing to do a lot of dirty talking and learn various naughty sexual antics.
5 Considerations Before Becoming a Phone Sex Operator
- It is not a full-time job but rather just a part-time gig to help generate some extra cash flow into your budget.
- Don’t trust websites that require you to pay a start-up fee and promises you things that are too good to be true. These are just scammers.
- Prepare yourself for an interview and audition. The interview will give you a chance to ask questions and inquire about the rates. And the audition is an opportunity for you to showcase what you can offer.
- Use an alias. Don’t use your real name when talking to your callers or clients. Choose only one alias and stick to that name for easy recall.
- Look only for reputable and trustworthy companies and websites. Some websites that you can explore are Adultstaffing and Sexyjobs.


